An optimal content indexing approach for named data networking in software‐ defined IoT system - Dudeja - 2022 - IET Smart Cities - Wiley Online Library

Remote Sensing | Free Full-Text | Data Fusion in Earth Observation and the Role of Citizen as a Sensor: A Scoping Review of Applications, Methods and Future Trends | HTML
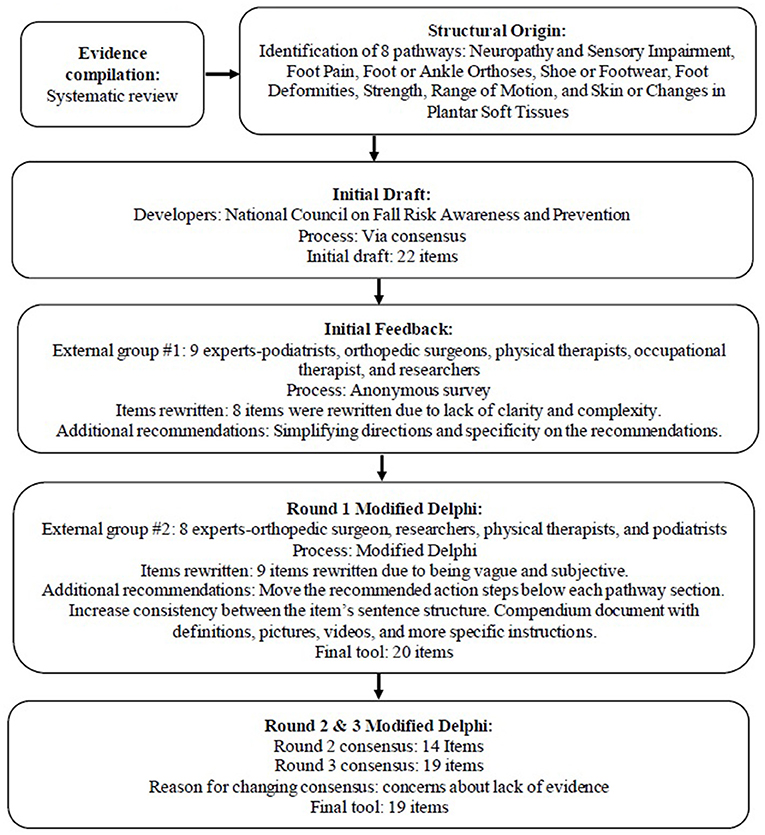
Frontiers | Feet/Footwear-Related Fall Risk Screening Tool for Older Adults: Development and Content Validation

A worked example of initial theory-building: PARTNERS2 collaborative care for people who have experienced psychosis in England - Ruth Gwernan-Jones, Nicky Britten, Jon Allard, Elina Baker, Laura Gill, Helen Lloyd, Tim Rawcliffe,
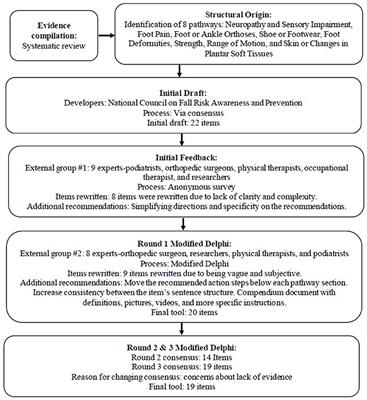
Frontiers | Feet/Footwear-Related Fall Risk Screening Tool for Older Adults: Development and Content Validation
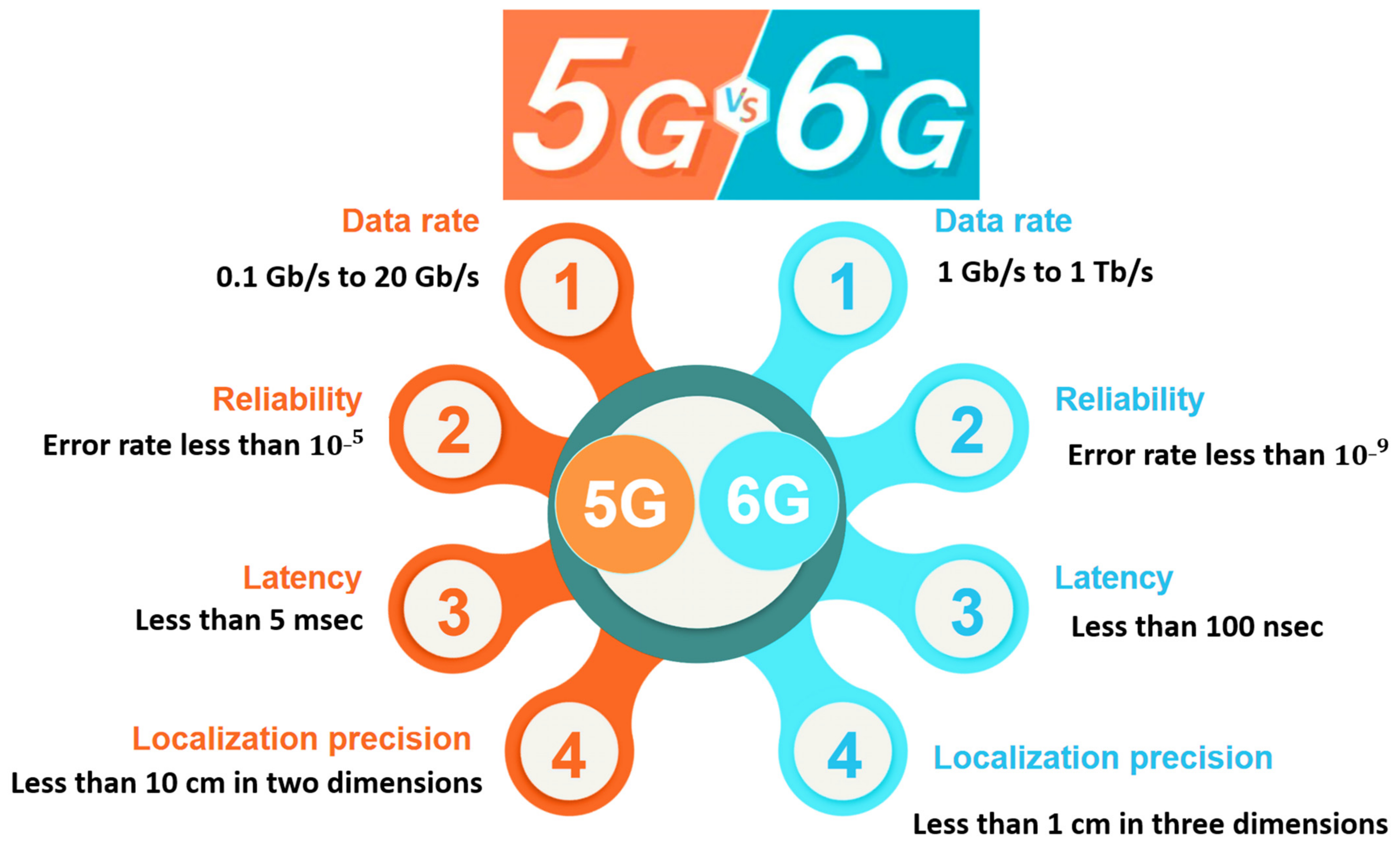
Sensors | Free Full-Text | Security Requirements and Challenges of 6G Technologies and Applications | HTML

Structure-based discovery of nonopioid analgesics acting through the α2A-adrenergic receptor | Science
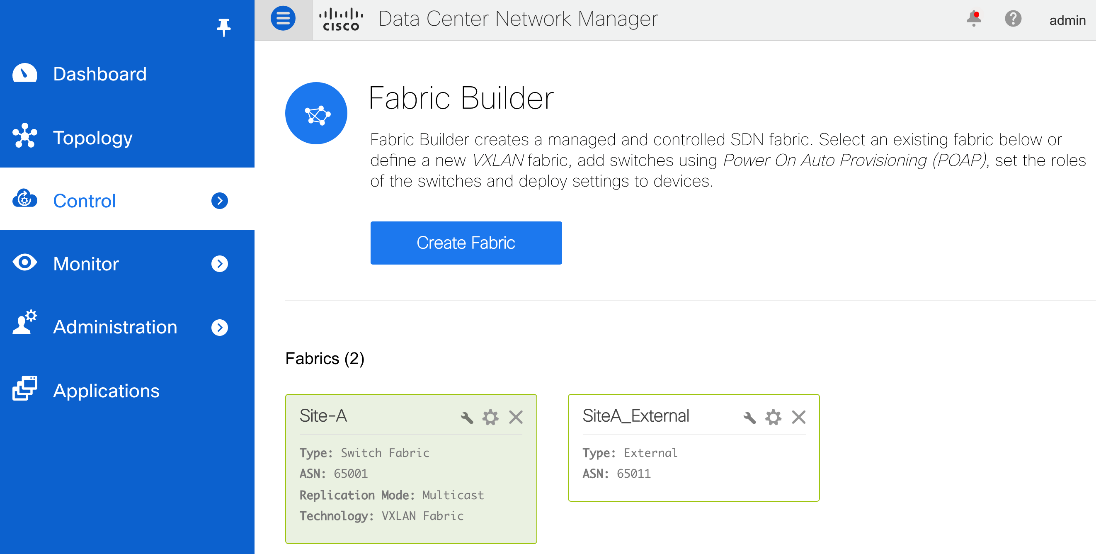
FlexPod Datacenter with VMware vSphere 7.0, Cisco VXLAN Single-Site Fabric, and NetApp ONTAP 9.7 - Cisco
![Cisco Wireless Control System Configuration Guide, Release 7.0 - Chapter 18: Administrative Tasks [Support] - Cisco Cisco Wireless Control System Configuration Guide, Release 7.0 - Chapter 18: Administrative Tasks [Support] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/200001-300000/250001-260000/251001-252000/251749.tif/_jcr_content/renditions/251749.jpg)
Cisco Wireless Control System Configuration Guide, Release 7.0 - Chapter 18: Administrative Tasks [Support] - Cisco
![Connected Communities Infrastructure Solution Implementation Guide - Connected Communities Infrastructure Solution Implementation Guide [Solutions] - Cisco Connected Communities Infrastructure Solution Implementation Guide - Connected Communities Infrastructure Solution Implementation Guide [Solutions] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/300001-400000/380001-390000/387001-388000/387570.jpg)
Connected Communities Infrastructure Solution Implementation Guide - Connected Communities Infrastructure Solution Implementation Guide [Solutions] - Cisco
3.12.179 Individual Master File (IMF), Payer Master File (PMF) Unpostable Resolution | Internal Revenue Service