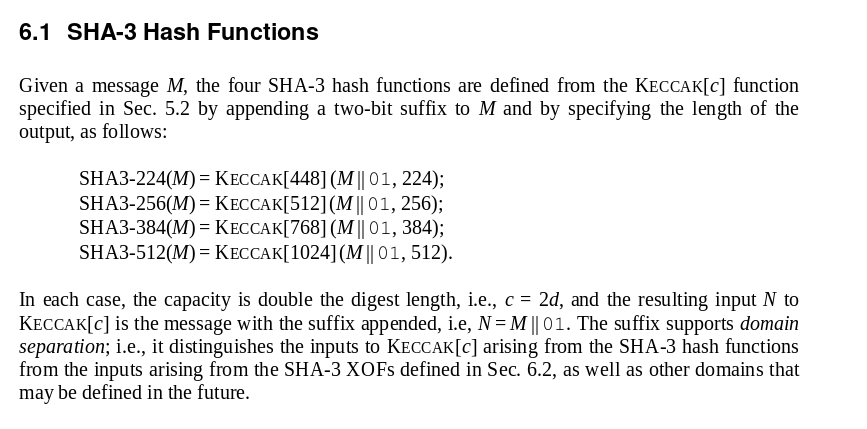
Design of a cryptographically secure pseudo random number generator with grammatical evolution | Scientific Reports

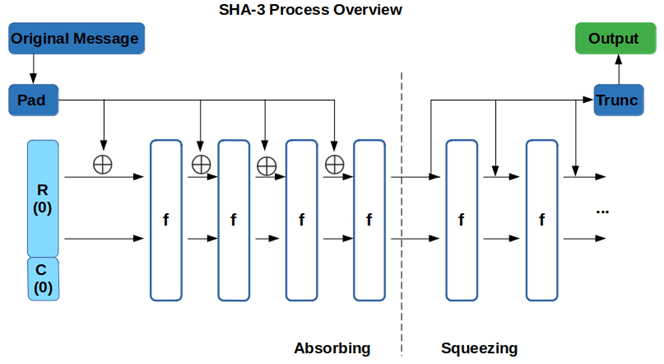
Test Implementation of SHA-3 Secure Hash Algorithm 3 by James Pate Williams, Jr. BA, BS, MSwE, PhD – Numerical Explorations
/filters:no_upscale()/news/2020/01/blake3-fast-crypto-hash/en/resources/1blake-3-crypto-hash-1-1578826134116.jpeg)