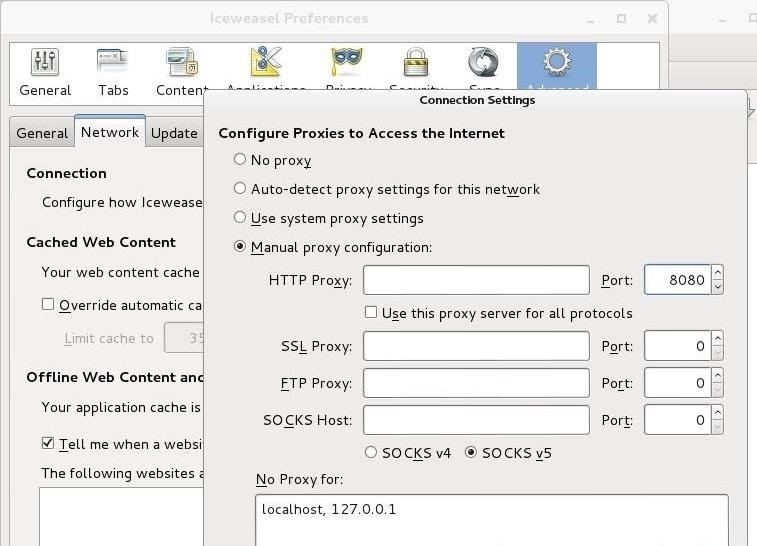
Hack Like a Pro: How to Crack Online Web Form Passwords with THC-Hydra & Burp Suite « Null Byte :: WonderHowTo

Proxy Re-Encryption — Allowing Alice To Share Her Protect Secret Key With Bob | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium
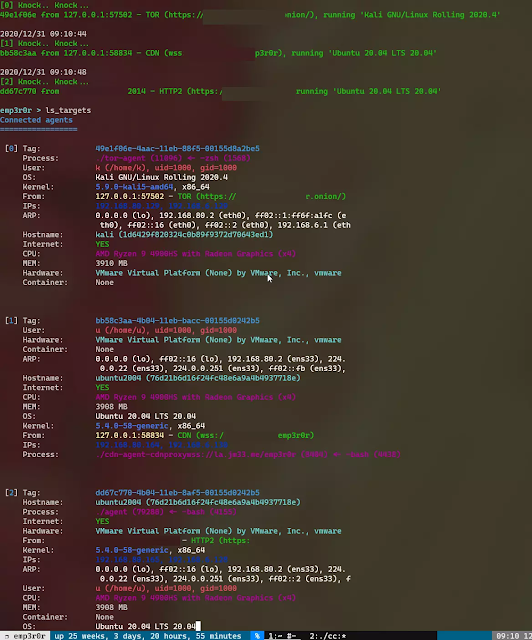
Emp3R0R - Linux Post-Exploitation Framework Made By Linux User - Hacking Land - Hack, Crack and Pentest
![NEW PROXO PET SIM X) [🏦 BANK] PET SIMULATOR X SCRIPT PASTEBIN!|UNLOCK ALL GAMEPASS AUTOFARM - YouTube NEW PROXO PET SIM X) [🏦 BANK] PET SIMULATOR X SCRIPT PASTEBIN!|UNLOCK ALL GAMEPASS AUTOFARM - YouTube](https://i.ytimg.com/vi/mdKgGh6xSlI/hqdefault.jpg)
NEW PROXO PET SIM X) [🏦 BANK] PET SIMULATOR X SCRIPT PASTEBIN!|UNLOCK ALL GAMEPASS AUTOFARM - YouTube